„Információs rendszerek üzemeltetése - Nagykérdések” változatai közötti eltérés
| 233. sor: | 233. sor: | ||
# Titkosítás: * '''!!!HIÁNYZIK!!!''' | # Titkosítás: * '''!!!HIÁNYZIK!!!''' | ||
Inkább ezek: | |||
* Confidentiality | |||
Confidentiality refers to preventing the disclosure of information to unauthorized individuals or systems. For example, a credit card transaction on the Internet requires the credit card number to be transmitted from the buyer to the merchant and from the merchant to a transaction processing network. The system attempts to enforce confidentiality by encrypting the card number during transmission, by limiting the places where it might appear (in databases, log files, backups, printed receipts, and so on), and by restricting access to the places where it is stored. If an unauthorized party obtains the card number in any way, a breach of confidentiality has occurred. Confidentiality is necessary for maintaining the privacy of the people whose personal information a system holds. | |||
* Integrity | |||
In information security, data integrity means maintaining and assuring the accuracy and consistency of data over its entire life-cycle. This means that data cannot be modified in an unauthorized or undetected manner. This is not the same thing as referential integrity in databases, although it can be viewed as a special case of Consistency as understood in the classic ACID model of transaction processing. Integrity is violated when a message is actively modified in transit. Information security systems typically provide message integrity in addition to data confidentiality. | |||
* Availability | |||
For any information system to serve its purpose, the information must be available when it is needed. This means that the computing systems used to store and process the information, the security controls used to protect it, and the communication channels used to access it must be functioning correctly. High availability systems aim to remain available at all times, preventing service disruptions due to power outages, hardware failures, and system upgrades. Ensuring availability also involves preventing denial-of-service attacks. | |||
=== 25. Milyen funkciójú DNS szerverek ismertek egy Intranet infrastruktúrában, és mi a szerepük? === | === 25. Milyen funkciójú DNS szerverek ismertek egy Intranet infrastruktúrában, és mi a szerepük? === | ||
A lap 2013. május 30., 09:39-kori változata
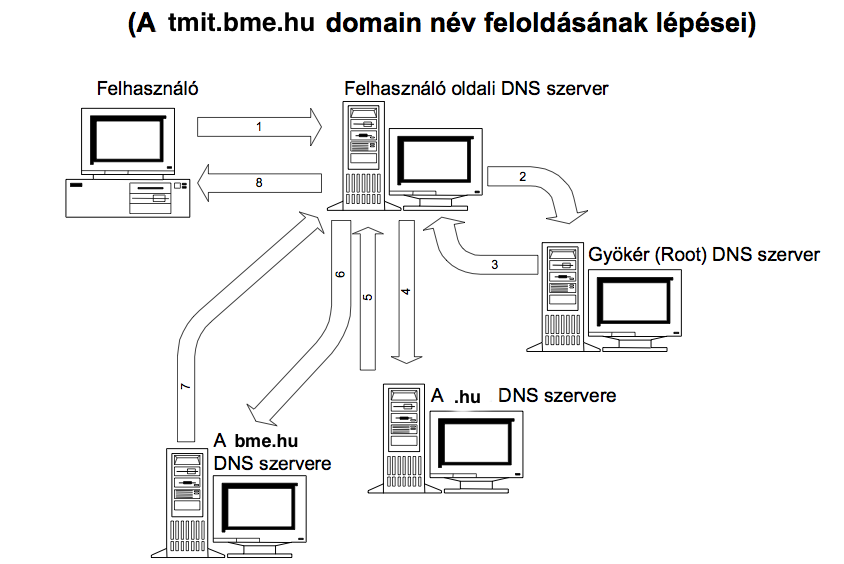
1. Írja le a tmit.bme.hu címének a lekérésének üzenetváltását, feltéve, hogy a cachek üresek!
| Sorszám | Küldő | Fogadó |
|---|---|---|
| 1 | Felhasználó | Felhasználó oldali DNS szerver |
| 2 | Felhasználó oldali DNS szerver | Root DNS szerver |
| 3 | Root DNS szerver | Felhasználó oldali DNS szerver |
| 4 | Felhasználó oldali DNS szerver | .hu DNS szerver |
| 5 | .hu DNS szerver | Felhasználó oldali DNS szerver |
| 6 | Felhasználó oldali DNS szerver | .bme.hu DNS szerver |
| 7 | .bme.hu DNS szerver | Felhasználó oldali DNS szerver |
| 8 | felhasználó oldali DNS szerver | Felhasználó |
2. Hasonlítsa össze a Raid 10 és a Raid 5 biztonsági, és kapacitási szempontból. Írja le az előnyeiket, hátrányaikat.
Mindkettő n+1 redundáns megvalósítású, 5-nél jobb a kapacitáskihasználás (n db diszknél a kihasználtság 100*(n-1)/n százalék, míg 10-nél 50%). RAID 5 előnye, hogy a paritás elosztva van a diszkeken, ezért gyorsabb sebesség érhető el vele, de a meghibásodásnál a visszaállítás macerás. RAID 10-nál ha egy diszk meghibásodik, akkor az simán visszaállítható a tükrözéséből, illetve ez a leggyorsabb technika (RAID 01-el egyetemben). Illetve a RAID 10 drágább, mint a RAID 5.
3. SLA
Egy cég SLA-t köt egy szolgáltatóval. Írjál le 2-2 mérhető tulajdonságát (SLA miatt számonkérhető) a VoiPnak, és az FTPnek.... SLA szerinti külön-külön 2-2, ha egy tulajdonsághoz írtál 2-2 dolgot akkor nem fogadták el.
- !!!HIÁNYZIK!!!
Szolgáltatás 1000 felhasználóval, az átlagos párhuzamos felhasználószám ennek 10%-a, egy felhasználó 2048 kbps sávszélességet igényel. Mekkorára kell tervezni Mbpsbe?
- 2048 kbps / 1024 = 2Mbps az átlagos sávszélesség igény. 2.) 1000 user 10%-a az 1000 * 0.1 = 100 user. 3.) 100 * 2Mbps = 200 Mbps
4. IPMI
Írja le pár mondatban az IPMI-t.
- Intelligent Platform Management Interface.
- Számítógépek hardver és firmware eszközei számára határoz meg közös interfészeket, amelyekkel a rendszeradminisztrátor a rendszerek állapotát ellenőrzés alatt tarthatja és menedzselheti.
- Operációs rendszer független
- Adatszerkezetet és formátumot ír elő, de az implementáció változhat.
- Közvetlen csatornán képes riasztást küldeni a távoli géphez.
Egy IPMI szabvány szerint készített operációs rendszer leállt. Miknek lehet megvizsgálni, hogy működnek-e? a) DMA driver b) HDMI illesztő c) IEEE-illesztő? d) mindegyiket
Mindegyik, mert ilyenkor is elérhetővé teszi a rendszer alkotó részeiről az érintett adatokat.
5. Adatmentés
Egy 5 TB vinyó, 20% változik kb naponta, és differenciális mentést alkalmazunk. Milyen gyakran legyen a teljes mentés? Miért?
- Három naponta, mert első nap 1TB, második nap 2TB(1+1TB) ekkor összesen már 3TB-ot lementettünk. Harmadik nap 3TB-ot mentenénk, de eddig már ezzel együtt összesen 6TB-ot mentenénk, úgyhogy itt már érdemes 5TB-ot menteni teljes mentéssel.
Egy 5 TB vinyó, 10% változik naponta, a mentés-helyreállító rendszer sávszélesége 500GB/óra. Milyen mentési módszert alkalmazna, hogyha a cél egy hiba után egy tetszőleges nap LEHETŐ LEGGYORSABB visszaállítása.
- Teljes mentés, a gyorsaság miatt. Ha minden nap teljes mentést csinálsz, akkor egy kazetta felhasználásával bármelyik napot visszaállíthatod. Ha viszont differenciális mentést csinálnál, akkor az két kazetta. Inkrementálisnál pedig sok kazettacsere kell.
6. Táblázat kitöltés. Vasárnap teljes mentés volt, ki kellet tölteni, hogy a Differenciális, az Inkrementális, és a Progresszív miket ment hétfőn, kedden, és szerdán. Hétfőn az A file-t változtatták. Kedden az F file-t töröltük a B-t áthelyeztük. Szerdán a G-t létrehoztuk, és az D-t módosítottuk.
| Vasárnap | Hétfő | Kedd | Szerda |
|---|---|---|---|
| File A | File A módosítás | File A (módosított) | File A (módosított) |
| File B | FIle B | File B áthelyezése | File B (áthelyezett) |
| File D | File D | File D | File D módosítása |
| File F | File F | File F törlése | - |
| - | - | - | File G létrehozása |
| Fájlok a vasárnapi teljes mentéskor | Fájlok a hétfői inkrementális mentéskor | Fájlok a keddi inkrementális mentéskor | Fájlok a szerdai inkrementális mentéskor | Merevlemez szerdán visszaállítás után |
|---|---|---|---|---|
| File A | File A (módosított) | File A (módosított) | ||
| File B | File B (áthelyetett) | File B (áthelyezett) | ||
| File D | File D (módosított) | File D (módosított) | ||
| File F | File F (törölt) | |||
| File G (létrehozott) | File G (létrehozott) |
| Fájlok a vasárnapi teljes mentéskor | Fájlok a hétfői differenciális mentéskor | Fájlok a keddi differenciális mentéskor | Fájlok a szerdai differenciális mentéskor | Merevlemez szerdán visszaállítás után |
|---|---|---|---|---|
| File A | File A (módosított) | File A (módosított) | File A (módosított) | File A (módosított) |
| File B | File B (áthelyetett) | File B (áthelyetett) | File B (áthelyezett) | |
| File D | File D (módosított) | File D (módosított) | ||
| File F | File F (törölt) | File F (törölt) | ||
| File G (létrehozott) | File G (létrehozott) |
Fenti táblázatokban miért mentjük a törölt fájlt?? Áthelyezéskor az új helyen lévőt mentjük (régit nem).
| Fájlok a vasárnapi teljes mentéskor | Fájlok a hétfői progresszív mentéskor | Fájlok a keddi progresszív mentéskor | Fájlok a szerdai progresszív mentéskor | Merevlemez szerdán visszaállítás után |
|---|---|---|---|---|
| File A | File A (módosított) | File A (módosított) | ||
| File B | File B (áthelyetett) | File B (áthelyezett) | ||
| File D | File D (módosított) | File D (módosított) | ||
| File F | File F (törölt) | |||
| File G (létrehozott) | File G (létrehozott) | |||
| Fájlstruktúra: A, B, D, F | A, B, D, F | A, B, D | A, B, D, G | Helyreállításkor visszakereshető, hogy egy fájlnak melyik az aktuális állapota (időnyereség az inkrementálishoz képest) |
7. Ismertesse a logikai hozzáférés-kezelés három alapelvét.
- minimális hozzáférési info (need-to-know): a felhasználó csak annyi információt tudhat, ami feltétlenül szükséges a munkája ellátásához
- minimális jogosultság: a felhasználó a legszűkebb körű jogosultsággal rendelkezhet, amely elegendő a munkavégzéshez
- feladatok elhatárolása: egy személy nem lehet felelős egy tranzakciólánc több lépéséért
8. Virtualizáció 2 előnye/hátránya
- előnyei: közös erőforrás gazdálkodás, redundancia, magas rendelkezésre állás, új szerver gyors telepítése, leállás nélkül átkonfigurálható, fizikai erőforrások optimalizálása gazdaságos
- hátrányai: bonyolultabb tervezés, drágább konfiguráció
9. Intranet DNS szerverei
- lokális DNS cache szerver: gyorsítja a DNS rekordok feloldását, tárolja őket egy ideig, ha nem találja, akkor a root szervertől kéri le
- root DNS szerver: feloldja a hálózat számítógépei számára a DNS neveket, felveszi az Interneten lévő gépekkel a kapcsolatot, stb.
10. Differenciális+Inkrementális mentéses táblázat kitöltése, visszaállításra kérdés (szombaton a csütörtöki napot állítjuk vissza, melyik szalagok kellenek, melyik szalagról melyik fájlokat állítjuk vissza)
- differenciális: ciklus első napján teljes mentés, utána minden nap csak az előző teljes mentés óta történt változásokat mentjük
- inkrementális: ciklus első napján teljes mentés, utána minden nap csak az előző mentés óta történt változásokat mentjük
- Táblázat: !!!HIÁNYZIK!!!
11. Hibajegyek kitöltése a megadott szabályok alapján, plusz új szabály kitalálása
- !!!HIÁNYZIK!!!
12. Felhő IT 5 alapelve
- internet protokollokkal elérhető bármely számítógépről
- mindig elérhető és az igényekhez igazítható
- felhasználás szerint fizetett
- vezérlő/ellenőrző interfészek
- „önkiszolgáló”
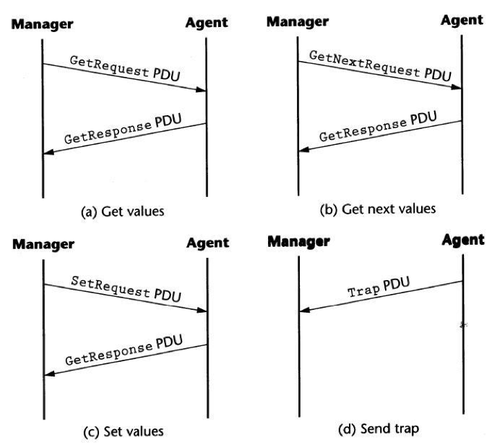
13. SNMP üzenetek, típusai, mire valók, tipikus párbeszéd példa.
- Üzenetek
- Get-Request(0): egy van több értéket kér a Management Agent MIB-től.
- Get-Next-Request(1): A lexikografikus leírásban következő Object Identifier-t kéri a MIB fán belül úgy, hogy megadja a jelenlegi Object Identifier-t.
- Get-Response(2): Válasz az érték-kérésre.
- Set-Request(3): Beállítja az adott értéket (vagy feladatot) a menedzselt eszköz MIB-jében.
- Trap(4): Egy kéretlen üzenet a menedzselt eszköztől, amit egy ott beállított esemény triggerelt.
- Tipikus példa:
14. Van egy táblázat megadva adatokkal.
a) El kell dönteni milyen forgalmat jellemez.
- VoIP szokott lenni.
b) Mondani kell valamit a QoE-ről.
- Itt tapasztalati dolgokra kiváncsiak. A jitteres stb. nem jó. Szóval szakadozhat, recseghet, ilyesmi kell.
c) Hogyan küszöbölné ki a hibát?
- Magasabb prioritást kell neki adni.
15. Mentési stratégiás feladat. Vasárnap teljes mentés. Valamilyen sorrendben szerdáig A fájl módosítva lesz, B áthelyezve, D törölve, E módosítva, F létrehozva. Szerda esti állapotot akarunk visszaállítani. Ki kell tölteni 3 táblázatot az adott mentési stratégiának megfelelően.
- A diff és ink mentésnél megegyezik. Ezeknél a módosított, módosított lesz (nem átnevezésre emlékszem), az áthelyezett az eredeti és az áthelyezett helyen is lesz, míg a törölt megmarad. A progresszívnél minden helyesen lesz. Fontos az időrend betartása. A javító kérte volna a progresszív mentési stratégia lényegének leírását, ami nem szerepelt a feladat leírásban, reklamálást elfogadta, szóval elvileg mindenkinek járt az 1 pont. Nem a diák szerinti jelölés kell, hanem haáthelyez az tényleg áthelyezed másik cellába és nem pl. B (new folder). Erre adott szintén 1 pontot, mikor mondtam, hogy így csináltam. A módosítást nem tudom, hogy kell(-e) jelölni.
16. Jitter-buffer számolás.
a) 24 frames/s-es video szolgáltatás. 24 Mbite/s-es vonalon. SLS 0.25 sec-es max késleltetést garantál. A hálózat 0.05 sec-es késleltetést ad max. Mekkora buffer kell a kliensnek(?)?
- Ki kell vonni az SLS-ből a hálózatit. 0.2 sec. Ezt kell beszorozni az átviteli sebességgel: 4.8Mbit.
b) Mekkora jitter-buffer kell, ha 1000 felhasználónk van, akinek átlag 20%-a használja egyidejűleg a szolgáltatást?
- 1000 főre vállaltunk, akkor annyira kell számolni. Így elvileg 1000*4.8=4800Mbit
17. Hogyan védekezne adatszivárgás ellen?
- Hordozható eszközök felügyelete meg tiltása. Még valami kellett, mert pirossal oda volt írva a javításon.
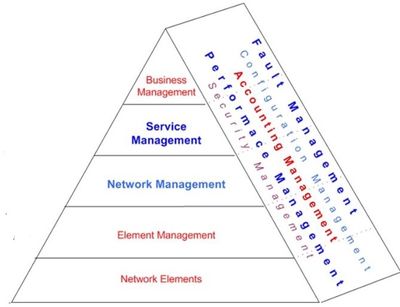
18. Rajzolja fel a TMN logikai modellt és nevezze meg az elemeit!
- Business Mgmt, Service Mgmt, Network Mgmt, Element Mgmt, Network Element
- Fault Mgmt, Configuration Mgmt, Accounting Mgmt, Performance Mgmt, Security Mgmt
19. FCAPS-nál minden funkcióhoz nevezzen meg példaképpen egy eszközt, ami megvalósítja.
- F(ault Management): SMTP helyett SNMP :DD
- C(onfiguration Management): eszköz- és raktáradatbázis
- A(ccounting Management): felhasználói statisztikák
- P(erformance Management): QoS, SLA
- S(ecurity Management): tűzfal
20. Egy IPMI szabvány szerint készített számítógépet az Operációs rendszer (nemtudom milyenm gixere után). Megállapítható-e, az alábbi komponensek működőképessége. Alaplapi diszk vezérlő / Alaplapi grafikus kártya / LAN vezérlő.
- * !!!HIÁNYZIK!!!
21. FlashCopy számolós táblázat.
- !!!HIÁNYZIK!!!
22. Ismertesse a logikai hozzáférés-kezelés három alapelvét.
- minimális hozzáférési infó
- minimális jogosultság
- feladatok elhatárolása
23. Listázza ki a logikai hozzáférés kezelés elvein belül a jelszókezeléssel kapcsolatban felmerülő problémákat.
- Alapértelmezett jelszó
- Ideiglenes jelszó
- Egyszer használatos jelszó
- Jelszó öregedés
- Nem tárolható, továbbítható titkosítatlanul
- Erős jelszavak használata
- Probléma, ha: túl komplex a jelszó, túl gyakran kell változtatni
- 3 próbálkozás után felhasználó kizárása
24. Mi az adattitkosítás három fő feladata? Jellemezze mindegyik 2-2 mondatban!
- Adatintegritás (ne lehessen megváltoztatni) * !!!HIÁNYZIK!!!
- Eredet azonosítás (tényleg attól származik, akinek mondja magát) * !!!HIÁNYZIK!!!
- Titkosítás: * !!!HIÁNYZIK!!!
Inkább ezek:
- Confidentiality
Confidentiality refers to preventing the disclosure of information to unauthorized individuals or systems. For example, a credit card transaction on the Internet requires the credit card number to be transmitted from the buyer to the merchant and from the merchant to a transaction processing network. The system attempts to enforce confidentiality by encrypting the card number during transmission, by limiting the places where it might appear (in databases, log files, backups, printed receipts, and so on), and by restricting access to the places where it is stored. If an unauthorized party obtains the card number in any way, a breach of confidentiality has occurred. Confidentiality is necessary for maintaining the privacy of the people whose personal information a system holds.
- Integrity
In information security, data integrity means maintaining and assuring the accuracy and consistency of data over its entire life-cycle. This means that data cannot be modified in an unauthorized or undetected manner. This is not the same thing as referential integrity in databases, although it can be viewed as a special case of Consistency as understood in the classic ACID model of transaction processing. Integrity is violated when a message is actively modified in transit. Information security systems typically provide message integrity in addition to data confidentiality.
- Availability
For any information system to serve its purpose, the information must be available when it is needed. This means that the computing systems used to store and process the information, the security controls used to protect it, and the communication channels used to access it must be functioning correctly. High availability systems aim to remain available at all times, preventing service disruptions due to power outages, hardware failures, and system upgrades. Ensuring availability also involves preventing denial-of-service attacks.
25. Milyen funkciójú DNS szerverek ismertek egy Intranet infrastruktúrában, és mi a szerepük?
- Lokális DNS cache szerver: gyorsítja a DNS rekordok feloldását, tárolja őket egy ideig, ha nem találja, akkor a Root szervertől kéri le
- Root DNS szerver: feloldja a hálózat számítógépei számára a DNS neveket, felveszi az Interneten lévő gépekkel a kapcsolatot, stb
26. Hálózatunkban (A:24, B:25) frame/sec, (A:2.4, B:2.5) Mbps paraméterű videóstreaming szolgáltatás működtetést vállaltunk, melynél a késleltetés mindig 0.25s lehet maximum. A hálózati eszközök az átviteli úton maximum 0.05 másodperc késleltetést okoznak. A csomagvesztés elhanyagolható.
a) A fenti adatok ismeretében mekkorára méretezné a jitter-buffer és miért?
- 0.25s - 0.05s = 0.2s késleltetést okozhatunk mi. (A:2.4 * 0.2 = 0.48???, B:2.5 * 0.2 = 0.5) Mb méretű buffer kell.
b) Ha a hálózatban 1000 videó letöltő felhasználó van, de átlagosan csak a 20%-a használja egy időben a szolgáltatást, akkor mekkora memóriaterületet foglalna le a teljes szolgáltatás jitter-bufferének?
- 1000 letöltő, egyszerre 20%, DE mivel 1000re vállaltunk garanciát, ezért 1000-nek kell helyet foglalni => Tehát összes bufferméret (A:0.48*1000 = 480, B:0.5*1000 = 500) Mb.
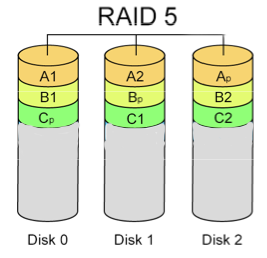
27. RAID 5, XOR
a) Rajzolja fel a lehető legkevesebb diszkből álló RAID 5 összeállítást!
- Minimum 3 diszk kell (http://en.wikipedia.org/wiki/RAID#Comparison)
b) XOR számolós feladat
- Alaphelyzet:
- DiskA: 0101101010101101
- DiskB: kiesett
- DiskP (Paritás disk): 0111010110111101
- Megoldás:
- DiskB = DiskA XOR DiskP
- 0101101010101101
- 0111010110111101
- --------------------------- (XOR)
- 0010111100010000 = DiskB
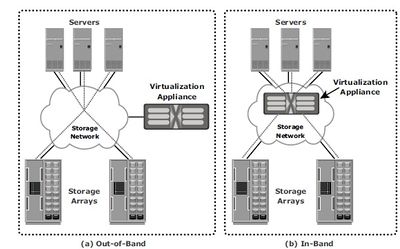
29. In-band és out-of-band tároló virtualizációs megoldások felrajzolása, összehasonlítása, előnyök, hátrányok
- In-Band: Virtualizáció motor az adatútban. lassab. szerveren nem kell speciális szoftver
- Out-of-band: Elválik egymástól a vezérlés és az adatút. gyorsabb, hiszen direkt hozzáfér az adattárolóhoz. Szükséges szoftver a szerverre ami lekérdezi a VM-től az adat fizikai helyét (utána meg eléri).